Abstract
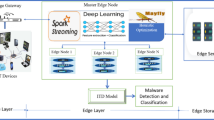
The accelerated growth of Internet of Things (IoT) devices and their convergence with Mobile Edge Computing (MEC) networks has transformed healthcare, smart cities, and industrial automation among other sectors. Nonetheless, this development presents notable security vulnerabilities, including Distributed Denial of Service (DDoS) and zero-day attacks against resource-limited edge nodes. This work puts forward a new hybrid deep learning model combining Convolutional Neural Networks (CNN) and Long Short-Term Memory (LSTM) networks to improve real-time anomaly detection in MEC-based IoT deployments. The proposed model can capture both the spatial and temporal features in network traffic patterns and allow accurate malicious pattern classification. Experiments are conducted using the publicly released IoT-23 dataset, which contains real-world traffic samples from compromised and benign IoT devices. The data was preprocessed with information and ratio-based feature selection techniques. It was implemented in Python with TensorFlow libraries to support scalable and efficient training of the model. The suggested model exhibited a remarkable improvement in detection performance in terms of classification accuracy, achieved an accuracy of 99%, outperforming conventional 1D CNN and gradient boosting models in terms of detection performance. Experimental outcomes indicate that the CNN-LSTM model is capable of accurately identifying DDoS attacks with fewer false positives and higher recall, rendering it ideal for real-time deployment in edge computing contexts. The model’s versatility with lightweight processing enables it to be a resilient security solution for IoT systems of the future.









Similar content being viewed by others
Data availability
No datasets were generated or analysed during the current study.
References
Nagajayanthi B (2022) Decades of internet of things towards twenty-first century: a research-based introspective. Wireless Pers Commun 123(4):3661–3697
Chataut R, Phoummalayvane A, Akl R (2023) Unleashing the power of IoT: a comprehensive review of IoT applications and prospects in healthcare, agriculture, smart homes, smart cities, and industry 4.0. Sensors (Basel) 23(16):7194
Allioui H, Mourdi Y (2023) Exploring the full potentials of IoT for better financial growth and stability: a comprehensive survey. Sensors 23(19):8015
Islam MM, Nooruddin S, Karray F, Muhammad G (2022) Internet of things: device capabilities, architectures, protocols, and smart applications in healthcare domain. IEEE Internet Things J 10(4):3611–3641
Hazra A, Rana P, Adhikari M, Amgoth T (2023) Fog computing for next-generation internet of things: fundamental, state-of-the-art and research challenges. Comput Sci Rev 48:100549
Saovapakhiran B, Naruephiphat W, Charnsripinyo C, Baydere S, Özdemir S (2022) Qoe-driven IoT architecture: a comprehensive review on system and resource management. IEEE Access 10:84579–84621
Haibeh LA, Yagoub MC, Jarray A (2022) A survey on mobile edge computing infrastructure: design, resource management, and optimization approaches. IEEE Access 10:27591–27610
Yang J, Shah AA, Pezaros D (2023) A survey of energy optimization approaches for computational task offloading and resource allocation in MEC networks. Electronics 12(17):3548
Mohiuddin K, Fatima H, Khan MA, Khaleel MA, Nasr OA, Shahwar S (2022) Mobile learning evolution and emerging computing paradigms: an edge-based cloud architecture for reduced latencies and quick response time. Array 16:100259
Gür G et al (2022) Integration of ICN and MEC in 5G and beyond networks: mutual benefits, use cases, challenges, standardization, and future research. IEEE Open J Commun Soc 3:1382–1412
Zhukabayeva T, Zholshiyeva L, Karabayev N, Khan S, Alnazzawi N (2025) Cybersecurity solutions for industrial internet of things–edge computing integration: challenges, threats, and future directions. Sensors 25(1):213
Ali MH et al (2022) Threat analysis and distributed denial of service (DDoS) attack recognition in the internet of things (IoT). Electronics 11(3):494
Shah Z, Ullah I, Li H, Levula A, Khurshid K (2022) Blockchain-based solutions to mitigate distributed denial of service (DDoS) attacks in the internet of things (IoT): a survey. Sensors 22(3):1094
Singh S, Sharma PK, Moon SY, Park JH (2024) Advanced lightweight encryption algorithms for IoT devices: survey, challenges and solutions. J Ambient Intell Humaniz Comput, pp. 1–18
Garg S, Kaur K, Kaddoum G, Garigipati P, Aujla GS (2021) Security in IoT-driven mobile edge computing: new paradigms, challenges, and opportunities. IEEE Netw 35(5):298–305. https://doi.org/10.1109/MNET.211.2000526
Bhat SA, Sofi IB, Chi C-Y (2020) Edge computing and its convergence with blockchain in 5G and beyond: security, challenges, and opportunities. IEEE Access 8:205340–205373. https://doi.org/10.1109/ACCESS.2020.3037108
Moudoud H, Khoukhi L, Cherkaoui S (2021) Prediction and detection of FDIA and DDoS attacks in 5G enabled IoT. IEEE Netw 35(2):194–201. https://doi.org/10.1109/MNET.011.2000449
Wu Y, Dai H-N, Wang H (2021) Convergence of blockchain and edge computing for secure and scalable IIoT critical infrastructures in industry 4.0. IEEE Internet Things J 8(4):2300–2317. https://doi.org/10.1109/JIOT.2020.3025916
Zhang L, Peng M, Wang W, Jin Z, Su Y, Chen H (2021) Secure and efficient data storage and sharing scheme for blockchain-based mobile‐edge computing. Trans Emerging Tel Tech 32(10):e4315. https://doi.org/10.1002/ett.4315
Li J, Wu J, Chen L, Li J, Lam S-K (2023) Blockchain-based secure key management for mobile edge computing. IEEE Trans Mobile Comput 22(1):100–114. https://doi.org/10.1109/TMC.2021.3068717
Hanif S, Ilyas T, Zeeshan M Intrusion detection in IoT using artificial neural networks on UNSW-15 dataset, in (2019) IEEE 16th International Conference on Smart Cities: Improving Quality of Life using ICT & IoT and AI (HONET-ICT), IEEE, 2019, pp. 152–156
Sahu AK, Sharma S, Tanveer M, Raja R (2021) Internet of things attack detection using hybrid deep learning model. Comput Commun 176:146–154
Osamor F, Wellman B (2022) Deep Learning-based hybrid model for efficient anomaly detection. Int J Adv Comput Sci Appl, 13, 4
Taha AA, Malebary SJ (2020) An intelligent approach to credit card fraud detection using an optimised light gradient boosting machine. IEEE Access 8:25579–25587
Trivedi NK, Simaiya S, Lilhore UK, Sharma SK (2020) An efficient credit card fraud detection model based on machine learning methods. Int J Adv Sci Technol 29(5):3414–3424
Azizjon M, Jumabek A, Kim W (2020) 1D CNN-based network intrusion detection with normalization on imbalanced data, in 2020 International Conference on Artificial Intelligence in Information and Communication (ICAIIC), IEEE, pp. 218–224
Acknowledgements
During the manuscript’s conception methodology design and drafting Suguna Krishnamoorhty contributed. Additionally, data interpretation and analysis were done. • Lekhavani and Suguna Krishnamoorthy carried out the experiments and gathered the data. helped with the manuscript’s revision and analysis. • Ramalakshmi Subbarayalu oversaw the research process evaluated the final draft and offered crucial insights during the study design. • Lack of resources for funding acquisition and project management in general. helped with the manuscripts’ proofreading and approval.
Funding
This research received no specific grant from any funding agency in the public, commercial, or not-for-profit sectors.
Author information
Authors and Affiliations
Contributions
During the manuscript’s conception methodology design and drafting Suguna Krishnamoorhty contributed. Additionally, data interpretation and analysis were done. • Lekhavani and Suguna Krishnamoorthy carried out the experiments and gathered the data. helped with the manuscript’s revision and analysis. • Ramalakshmi Subbarayalu oversaw the research process evaluated the final draft and offered crucial insights during the study design. Viyat Varun Upadhyay and N. Naga Bhooshanam were responsible for data curation. Sathish Kannan and Seeniappan Kaliappan contributed to reviewing and editing the manuscript.Yogendra Thakur was responsible for visualization • Lack of resources for funding acquisition and project management in general. helped with the manuscripts’ proofreading and approval.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Krishnamoorthy, S., Ramesh, L., Subbarayalu, R. et al. Navigating the complex terrain of security challenges and crafting robust solutions in Mec-enabled IOT ecosystems for future societies. Peer-to-Peer Netw. Appl. 18, 296 (2025). https://doi.org/10.1007/s12083-025-02124-3
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1007/s12083-025-02124-3